🌉 bridged from https://fediscience.org/@rupdecat on the fediverse by https://fed.brid.gy/
https://www.wikipathways.org/#download
#bioinformatics #elixirnl




https://www.wikipathways.org/#download
#bioinformatics #elixirnl
🔥 Hot take (since I'm not at all operating like this currently): I actually think this might be a good idea? It would curb some of the biggest "research mills", where one PI […]
🔥 Hot take (since I'm not at all operating like this currently): I actually think this might be a good idea? It would curb some of the biggest "research mills", where one PI […]
https://mainzerbeobachter.com/2025/12/17/vragen-rond-de-jaarwisseling-2025/
RT = ❤️

https://mainzerbeobachter.com/2025/12/17/vragen-rond-de-jaarwisseling-2025/
RT = ❤️
📢 #ScienceJobs Really interesting #researchdata analytics post-doc with Thanasis Tsanas, https://www.darth-group.com, analysing #sleep and circadian data for mental health research.
This is part of the Wellcome-funded AMBIENT-BD project that our BioRDM also works […]
📢 #ScienceJobs Really interesting #researchdata analytics post-doc with Thanasis Tsanas, https://www.darth-group.com, analysing #sleep and circadian data for mental health research.
This is part of the Wellcome-funded AMBIENT-BD project that our BioRDM also works […]
In any kind of normal timeline this would have been stopped by regulators. Instead we let a single company become the sole gatekeeper for everything in #hpc .
In any kind of normal timeline this would have been stopped by regulators. Instead we let a single company become the sole gatekeeper for everything in #hpc .
So, someone suggested I delete it, which I did. It took me a long time to recover. Now, I have re-written this blog post. I think it is better. I weighted every […]
So, someone suggested I delete it, which I did. It took me a long time to recover. Now, I have re-written this blog post. I think it is better. I weighted every […]
Echoing this critical advice, especially to #science organizations. If you are a science organization on Bluesky and you want to expand your audience to the open, federated social web, just follow this bridge account. Then I --- an […]
Echoing this critical advice, especially to #science organizations. If you are a science organization on Bluesky and you want to expand your audience to the open, federated social web, just follow this bridge account. Then I --- an […]
It only worked 1 time in a dozen or so trials.
If NCBI is getting instable, for whatever reason, is there an EU alternative?
The commands were like
`datasets download genome accession {params.accession} --include genome`
So, even […]
It only worked 1 time in a dozen or so trials.
If NCBI is getting instable, for whatever reason, is there an EU alternative?
The commands were like
`datasets download genome accession {params.accession} --include genome`
So, even […]
I attended the dry-run of this course* recently and it was pretty mind-blowing - I'd seen before how #pixi can be used for python packaging but this course introduced me to a few new example use cases:
- Reproducible data analysis […]
Alexander Dobrindt, NRW, Hessen, Bayern, BaWü: Lasst uns doch einfach die sensibelsten Daten der Bürger*innen genau von den Typen verwalten, die bei Trump am Tisch sitzen! 🤗
Alexander Dobrindt, NRW, Hessen, Bayern, BaWü: Lasst uns doch einfach die sensibelsten Daten der Bürger*innen genau von den Typen verwalten, die bei Trump am Tisch sitzen! 🤗
The #livestream will be on: https://stream.firesidefedi.live
Special Guest: @hfalcke
#Prof. #astrophysics, columnist D/NL, #bestseller #author 'Lim Dunkeln/Light in the Darkness/Licht in de […]
[Original post on social.firesidefedi.live]

The #livestream will be on: https://stream.firesidefedi.live
Special Guest: @hfalcke
#Prof. #astrophysics, columnist D/NL, #bestseller #author 'Lim Dunkeln/Light in the Darkness/Licht in de […]
[Original post on social.firesidefedi.live]
Chaque trimestre, la newsletter vous offrira un panorama complet des actualités, réflexions et ressources liées à la science ouverte sur le site lorrain : politiques […]
Chaque trimestre, la newsletter vous offrira un panorama complet des actualités, réflexions et ressources liées à la science ouverte sur le site lorrain : politiques […]
This was a yolo-release, I'm afraid: I am starting to dislike multicluster setups at #Slurm - the code base leaves something to be desired in terms of error messages and configuration flexibility. 😅
This was a yolo-release, I'm afraid: I am starting to dislike multicluster setups at #Slurm - the code base leaves something to be desired in terms of error messages and configuration flexibility. 😅

Lees pagina 25-27:
https://www.whitehouse.gov/wp-content/uploads/2025/12/2025-National-Security-Strategy.pdf

Lees pagina 25-27:
https://www.whitehouse.gov/wp-content/uploads/2025/12/2025-National-Security-Strategy.pdf
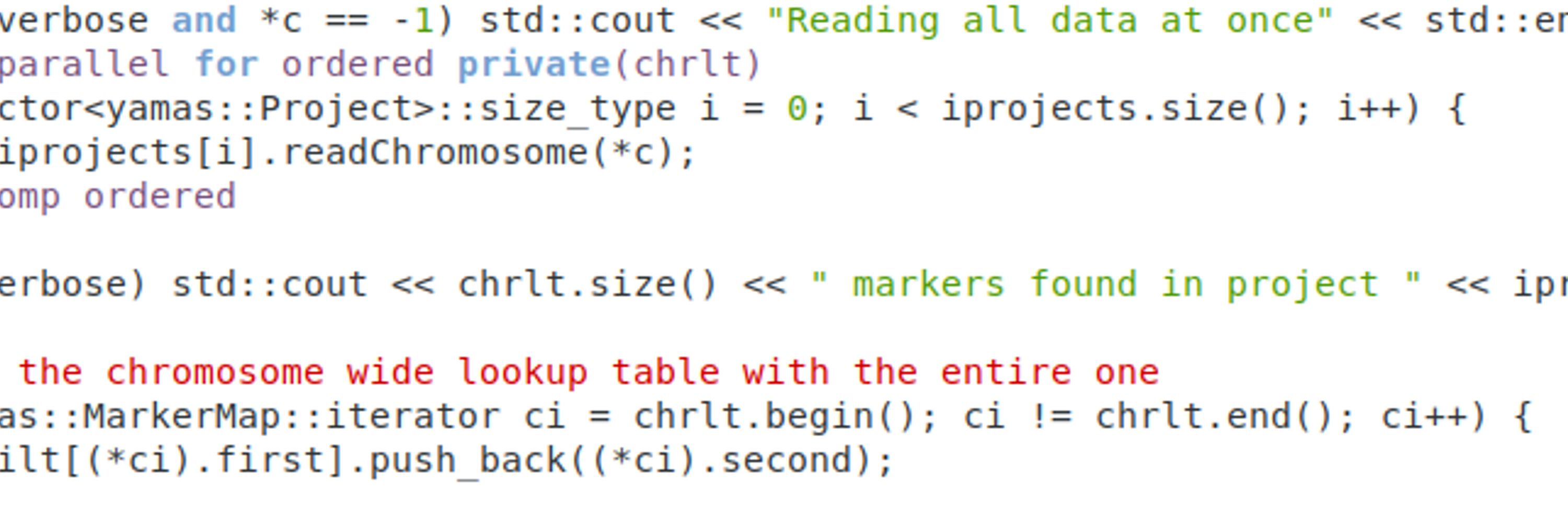
Today, after quite some tinkering, I managed to overly differential expression results. This is not stable code, yet. The […]
[Original post on fediscience.org]

Today, after quite some tinkering, I managed to overly differential expression results. This is not stable code, yet. The […]
[Original post on fediscience.org]
Plus que neuf jours pour trouver les quelques 574 € afin de poser la première pierre de Bonfire, fondation de Open Science Network, le premier réseau fédéré pour la communication scientifique, sous le contrôle des communautés scientifiques […]
Plus que neuf jours pour trouver les quelques 574 € afin de poser la première pierre de Bonfire, fondation de Open Science Network, le premier réseau fédéré pour la communication scientifique, sous le contrôle des communautés scientifiques […]

https://w3id.org/np/RAiFdv4D_zW85xY3e00XaxetTe2FQSt3nYzbuONj5TJ6M
Just, I don't think replying with another #nanopub is the way to go in a discussion. Right? And then: perhaps it is a good idea for space No.27 to work on an action plan? 😉
https://w3id.org/np/RAiFdv4D_zW85xY3e00XaxetTe2FQSt3nYzbuONj5TJ6M
Just, I don't think replying with another #nanopub is the way to go in a discussion. Right? And then: perhaps it is a good idea for space No.27 to work on an action plan? 😉
on Monday we have a go/no-go and we really want to go
So, are you considering sign up before Sunday evening!
#ontologies #linkeddata #sparql
Don't miss this exciting opportunity for Life Sciences researchers and data enthusiasts. In just 9 weeks, BioSB will host this course: https://www.dtls.nl/courses/knowledge-graphs-in-the-life-sciences-2026/
📅 January 5–9, 2025
🗺️ […]
on Monday we have a go/no-go and we really want to go
So, are you considering sign up before Sunday evening!
#ontologies #linkeddata #sparql
There are an incredibly large number of reasons why that is totally not going to work. But here's another from Borloff et al "Satellite […]
There are an incredibly large number of reasons why that is totally not going to work. But here's another from Borloff et al "Satellite […]

