#CyberSafety #HolidaySecurity #Thanksgiving #JANUSAssociates #Infosec #cybersecurity

#CyberSafety #HolidaySecurity #Thanksgiving #JANUSAssociates #Infosec #cybersecurity
If you want real intelligence (not hype) subscribe to the JANUS Cyber Threat Report for expert-led updates.
#Cybersecurity #ThreatIntel #Community

If you want real intelligence (not hype) subscribe to the JANUS Cyber Threat Report for expert-led updates.
#Cybersecurity #ThreatIntel #Community
www.infosecurity-magazine.com/news/chinese...
#cyberattacks #ai #code #anthropic #cybersecurity

www.infosecurity-magazine.com/news/chinese...
#cyberattacks #ai #code #anthropic #cybersecurity
~50% of attacks target SMBs, and 60% close after a breach.
Stay protected. Cybersecurity is essential for every business. #Cybersecurity #SmallBusiness #DataProtection #JanusAssociates

~50% of attacks target SMBs, and 60% close after a breach.
Stay protected. Cybersecurity is essential for every business. #Cybersecurity #SmallBusiness #DataProtection #JanusAssociates

JANUS Associates delivers proactive protection for law firms and SMBs using multi-factor authentication, behavior analytics, and a culture of vigilance.
#lawfirm #smb #cybersecurity #infosec #mfa

JANUS Associates delivers proactive protection for law firms and SMBs using multi-factor authentication, behavior analytics, and a culture of vigilance.
#lawfirm #smb #cybersecurity #infosec #mfa
#JanusAssociates CEO Patricia Fisher joins #CTTechnologyCouncil, #CONNSTEP, and leading experts on Thursday November 20, 2025 to show how compliance delivers competitive advantage. #cybersecurity #leadership #compliance #Connecticut

#JanusAssociates CEO Patricia Fisher joins #CTTechnologyCouncil, #CONNSTEP, and leading experts on Thursday November 20, 2025 to show how compliance delivers competitive advantage. #cybersecurity #leadership #compliance #Connecticut

This weak credential highlights how critical strong password policies and layered security are in protecting priceless assets.
Protecting your crown jewels requires next-level defense. #Cybersecurity #JANUSInsights #Louvre #Password
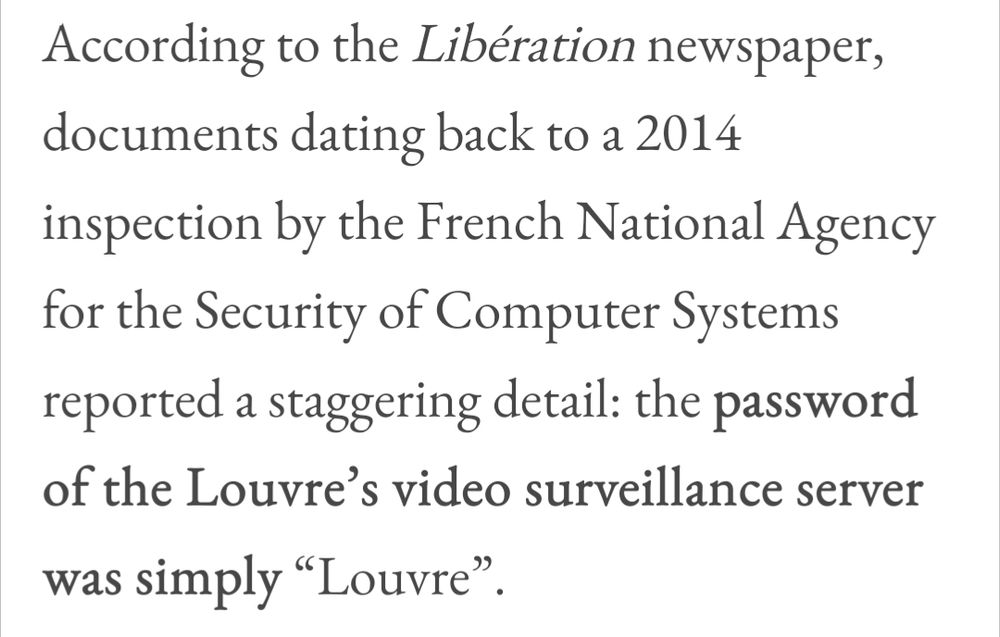
This weak credential highlights how critical strong password policies and layered security are in protecting priceless assets.
Protecting your crown jewels requires next-level defense. #Cybersecurity #JANUSInsights #Louvre #Password
Read now: info.janusassociates.com/blog/cyber-t...
#Cybersecurity #ThreatReport #InfoSec #RiskManagement #DataProtection #LatestNews

Read now: info.janusassociates.com/blog/cyber-t...
#Cybersecurity #ThreatReport #InfoSec #RiskManagement #DataProtection #LatestNews
With 35+ years of expertise, JANUS Associates can help you secure your future.
#Cybersecurity #DataProtection #BusinessSecurity
With 35+ years of expertise, JANUS Associates can help you secure your future.
#Cybersecurity #DataProtection #BusinessSecurity
At JANUS Associates, we know the real monsters aren’t wearing costumes: they’re hiding in your systems, inboxes, and blind spots. Don’t let tricks turn into disasters.

At JANUS Associates, we know the real monsters aren’t wearing costumes: they’re hiding in your systems, inboxes, and blind spots. Don’t let tricks turn into disasters.

JANUS October Cyber Threat Report dives into how AI social engineering has overtaken ransomware plus new insights on cloud and DDoS risks.
#CyberSecurity #AIThreats #InfoSec #ThreatIntel #ZeroTrust #CyberResilience

JANUS October Cyber Threat Report dives into how AI social engineering has overtaken ransomware plus new insights on cloud and DDoS risks.
#CyberSecurity #AIThreats #InfoSec #ThreatIntel #ZeroTrust #CyberResilience

