

my mother-in-law lives near Stroudsburg PA and is being cut off from streaming services because the geo-ip company suddenly decided that "STH" now meant "Stockholm"...
its almost like the hints geo-ip uses weren't meant to actually be relied on

my mother-in-law lives near Stroudsburg PA and is being cut off from streaming services because the geo-ip company suddenly decided that "STH" now meant "Stockholm"...
its almost like the hints geo-ip uses weren't meant to actually be relied on


www.documentcloud.org/documents/25...
CC @josephcox.bsky.social

www.documentcloud.org/documents/25...
CC @josephcox.bsky.social
github.com/apple/darwin...

github.com/apple/darwin...
a simple buffer overflow leads to an unconstrained ret addr which is then set to be the xref of the flag prefix X-MAS

a simple buffer overflow leads to an unconstrained ret addr which is then set to be the xref of the flag prefix X-MAS
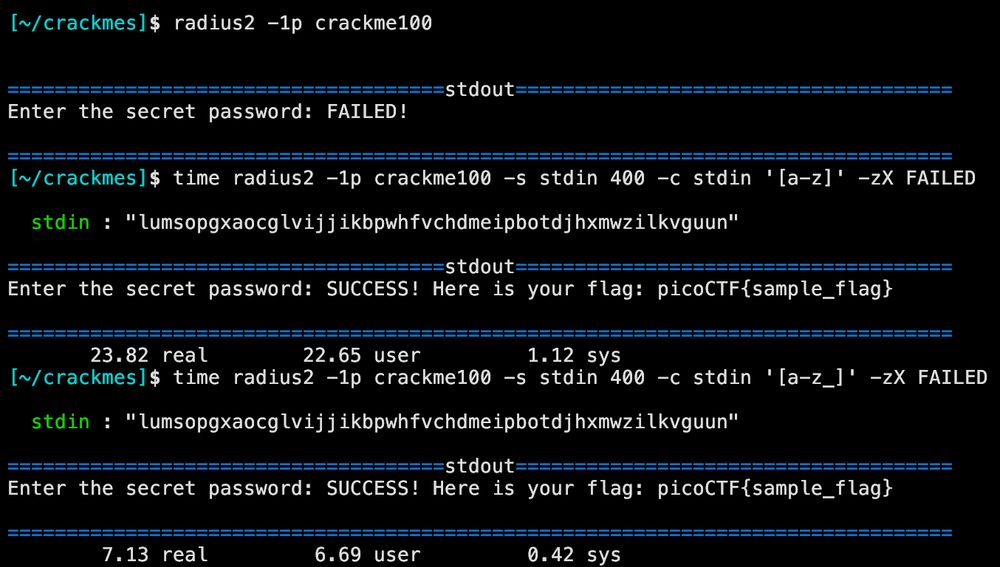
for a christmas gift to myself i will fix this and make a bunch of other radius2 improvements

for a christmas gift to myself i will fix this and make a bunch of other radius2 improvements







