Wannabe Red Teamer
AD/Entra enthusiast
@rastamouse.me pretty much predicted what was coming in his last blog post. attach (Win32 APIs), redirect (local funcs), capability right-sized IAT hooks, and PICO function exports.
Yes, attach can incept its PIC.
aff-wg.org/2025/11/10/t...

@rastamouse.me pretty much predicted what was coming in his last blog post. attach (Win32 APIs), redirect (local funcs), capability right-sized IAT hooks, and PICO function exports.
Yes, attach can incept its PIC.
aff-wg.org/2025/11/10/t...
aff-wg.org/2025/09/26/a...
Breach analysis? Breach intelligence? Industry critique? Fee-only ransomware negotiator? 100% efficacy? The story of how Microsoft worked an old problem, fucked it up, we malign the guy who told us, they fixed it, and it wasn't fixed? PtH?
aff-wg.org/2025/09/26/a...
Breach analysis? Breach intelligence? Industry critique? Fee-only ransomware negotiator? 100% efficacy? The story of how Microsoft worked an old problem, fucked it up, we malign the guy who told us, they fixed it, and it wasn't fixed? PtH?

aff-wg.org/2025/09/10/c...
A COFF-focused Crystal Palace update:
* internal COFF normalization & section group merging
* Crystal Palace can now export COFF
* I added COFF merging to the spec language too
Linker stuff.

aff-wg.org/2025/09/10/c...
A COFF-focused Crystal Palace update:
* internal COFF normalization & section group merging
* Crystal Palace can now export COFF
* I added COFF merging to the spec language too
Linker stuff.
@logangoins.bsky.social explains how to use HTTP-to-LDAP relay attacks to execute tooling completely off-host through the C2 payload context. Perfect for when you need LDAP access but want to avoid being caught stealing creds. ghst.ly/41mjMv7

@logangoins.bsky.social explains how to use HTTP-to-LDAP relay attacks to execute tooling completely off-host through the C2 payload context. Perfect for when you need LDAP access but want to avoid being caught stealing creds. ghst.ly/41mjMv7
Join 👉 ghst.ly/46MNltn
Join 👉 ghst.ly/46MNltn
@unsignedsh0rt.bsky.social unpacks his testing in his latest blog post. ghst.ly/4mjyuvw

@unsignedsh0rt.bsky.social unpacks his testing in his latest blog post. ghst.ly/4mjyuvw
Valdemar Carøe drops info on Certify 2.0, including a suite of new capabilities and refined usability improvements. ghst.ly/45IrBxI

Valdemar Carøe drops info on Certify 2.0, including a suite of new capabilities and refined usability improvements. ghst.ly/45IrBxI
github.com/olafhartong/...
Slides available here:
github.com/olafhartong/...
github.com/olafhartong/...
Slides available here:
github.com/olafhartong/...
Link: github.com/dirkjanm/adc...
Link: github.com/dirkjanm/adc...
blog.badsectorlabs.com/last-week-in...

blog.badsectorlabs.com/last-week-in...
Read more from @harmj0y.bsky.social: ghst.ly/4mxQzFU

Read more from @harmj0y.bsky.social: ghst.ly/4mxQzFU
sensepost.com/blog/2025/a-...
sensepost.com/blog/2025/a-...
@hotnops.bsky.social explores cross-domain compromise tradecraft within the same tenant.
Read more: ghst.ly/3ISMGN9

@hotnops.bsky.social explores cross-domain compromise tradecraft within the same tenant.
Read more: ghst.ly/3ISMGN9
Also includes ESC1 over Intune (in some cases).
dirkjanm.io/extending-ad...
Oh, and a new tool for SCEP: github.com/dirkjanm/sce...
Also includes ESC1 over Intune (in some cases).
dirkjanm.io/extending-ad...
Oh, and a new tool for SCEP: github.com/dirkjanm/sce...
This update introduces BloodHound OpenGraph, revolutionizing Identity Attack Path Management by exposing attack paths throughout your entire tech stack, not just AD/Entra ID.
Read more from Justin Kohler: ghst.ly/bloodhoundv8
🧵: 1/7
This update introduces BloodHound OpenGraph, revolutionizing Identity Attack Path Management by exposing attack paths throughout your entire tech stack, not just AD/Entra ID.
Read more from Justin Kohler: ghst.ly/bloodhoundv8
🧵: 1/7
blog.badsectorlabs.com/last-week-in...

blog.badsectorlabs.com/last-week-in...
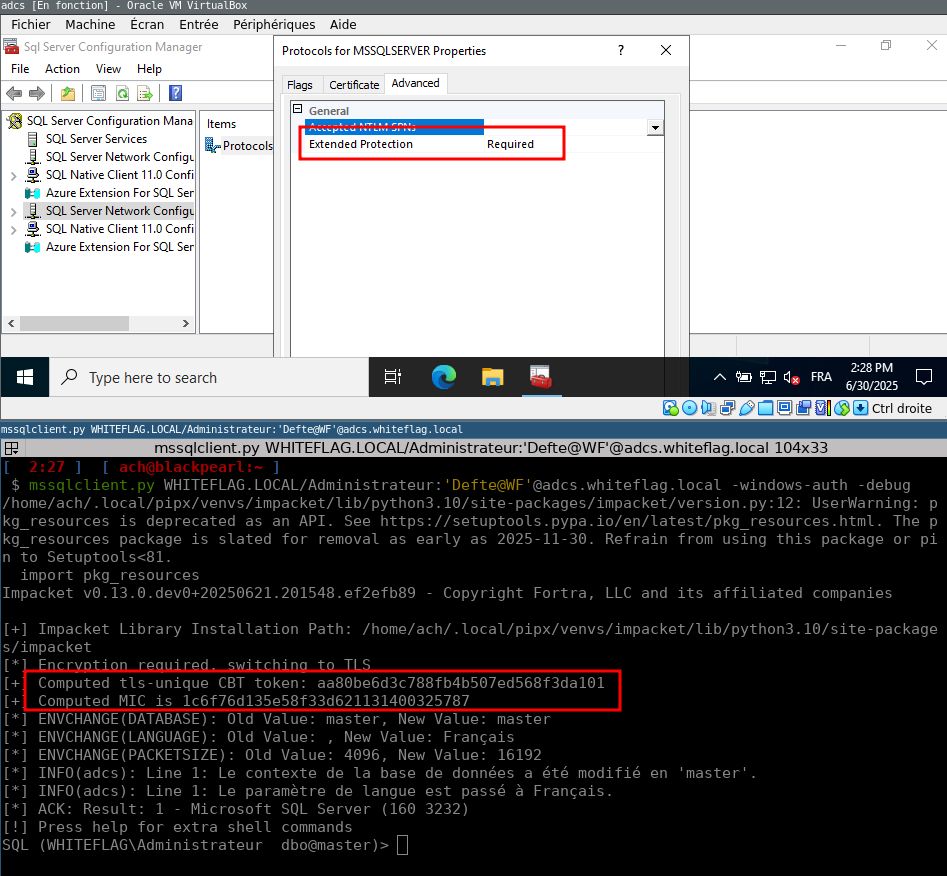
Alexander Sou explores why this is the current industry guidance. ghst.ly/40DTLHk

Alexander Sou explores why this is the current industry guidance. ghst.ly/40DTLHk
github.com/rasta-mouse/...
github.com/rasta-mouse/...
Here's the post - I demonstrate my QoL improvements for working with the TCG codebase. This includes vscode with intellisense support, and producing debug builds for use in WinDbg.
rastamouse.me/debugging-th...

Here's the post - I demonstrate my QoL improvements for working with the TCG codebase. This includes vscode with intellisense support, and producing debug builds for use in WinDbg.
rastamouse.me/debugging-th...
So what's a stealthy attacker to do? 🤔
Our latest blog post explores evasive alternatives beyond the old techniques. ghst.ly/3ILR1l0

So what's a stealthy attacker to do? 🤔
Our latest blog post explores evasive alternatives beyond the old techniques. ghst.ly/3ILR1l0
Multiple users can now edit observations, findings, & report fields simultaneously w/o the chaos of overwriting each other's work.
@printingprops.com dives into the details in his latest blog update. ghst.ly/3TTSrwc
Multiple users can now edit observations, findings, & report fields simultaneously w/o the chaos of overwriting each other's work.
@printingprops.com dives into the details in his latest blog update. ghst.ly/3TTSrwc
blog.badsectorlabs.com/last-week-in...

blog.badsectorlabs.com/last-week-in...
My thoughts (and code examples) for writing modular PIC C2 agents.
rastamouse.me/modular-pic-...

My thoughts (and code examples) for writing modular PIC C2 agents.
rastamouse.me/modular-pic-...


