Prince (CEO) explained that a feature file doubled in size. The larger-than-expected feature file was then propagated to all the machines that make up our network.”
arstechnica.com/tech-policy/...

Prince (CEO) explained that a feature file doubled in size. The larger-than-expected feature file was then propagated to all the machines that make up our network.”
arstechnica.com/tech-policy/...
November 18, 2025
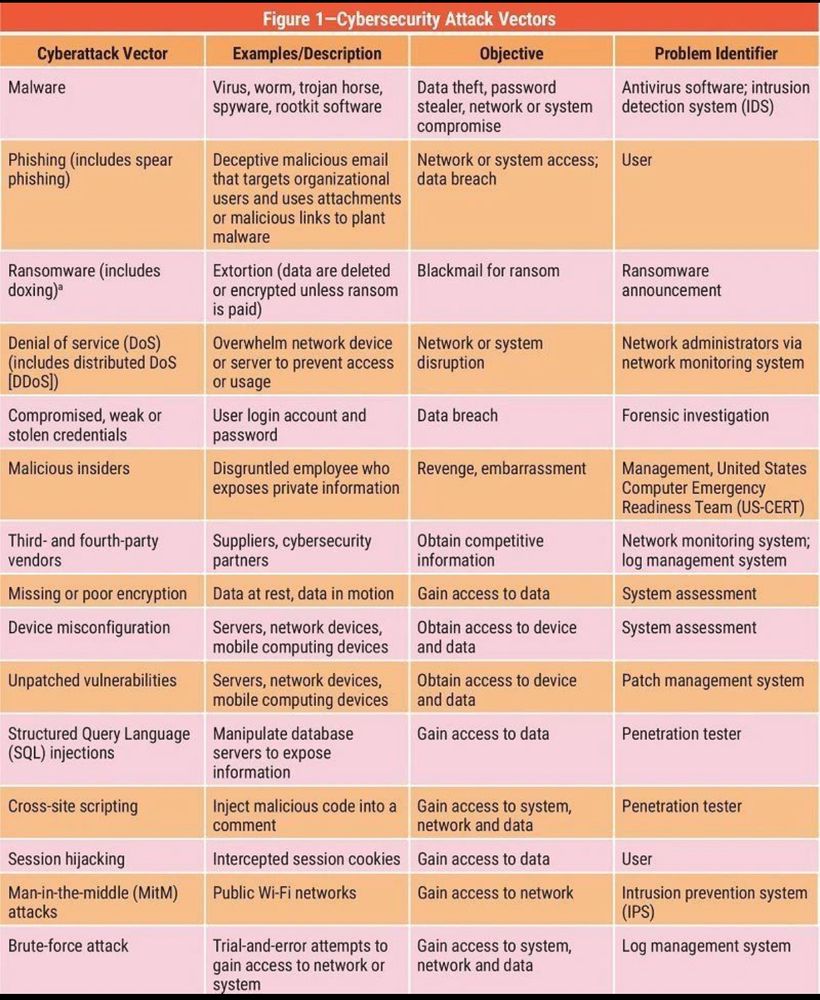
OWASP’s 2025 findings show broken access control remains one of the most persistent and damaging web security problems.
kbala97.github.io/CyberTechHea...

November 18, 2025
OWASP’s 2025 findings show broken access control remains one of the most persistent and damaging web security problems.
kbala97.github.io/CyberTechHea...
This article discusses common security vulnerabilities developers should be aware of when “vibe coding”—coding quickly without strict adherence to best practices. @harryguinness.bsky.social
kbala97.github.io/CyberTechHea...

This article discusses common security vulnerabilities developers should be aware of when “vibe coding”—coding quickly without strict adherence to best practices. @harryguinness.bsky.social
kbala97.github.io/CyberTechHea...
If you believe the hype, AI will soon take all our jobs, or solve all our problems, or destroy all boundaries between reality and lies. This brilliant podcast by @randomwalker.bsky.social Arvind Narayanan will help sort that out.
kbala97.github.io/CyberTechHea...

If you believe the hype, AI will soon take all our jobs, or solve all our problems, or destroy all boundaries between reality and lies. This brilliant podcast by @randomwalker.bsky.social Arvind Narayanan will help sort that out.
kbala97.github.io/CyberTechHea...
A paradox of security is that when you have invested appropriately and have less incidents, someone will ask: “Why are we spending on security when we don’t have any issues?"
@philvenables.bsky.social
kbala97.github.io/CyberTechHea...

A paradox of security is that when you have invested appropriately and have less incidents, someone will ask: “Why are we spending on security when we don’t have any issues?"
@philvenables.bsky.social
kbala97.github.io/CyberTechHea...
A great podcast to learn about what a “Solutions Architect” does and brings value! As always, a great podcast from Daliani Liu.
kbala97.github.io/CyberTechHea...

A great podcast to learn about what a “Solutions Architect” does and brings value! As always, a great podcast from Daliani Liu.
kbala97.github.io/CyberTechHea...
The current wave in AI is replacing task-specific models with those that are trained on a broad set of unlabeled data that can be used for different tasks, with minimal fine-tuning.
kbala97.github.io/CyberTechHea...

The current wave in AI is replacing task-specific models with those that are trained on a broad set of unlabeled data that can be used for different tasks, with minimal fine-tuning.
kbala97.github.io/CyberTechHea...
kbala97.github.io/CyberTechHea...

kbala97.github.io/CyberTechHea...
kbala97.github.io/CyberTechHea...

kbala97.github.io/CyberTechHea...
redmondmag.com/articles/202...

redmondmag.com/articles/202...
kbala97.github.io/CyberTechHea...
kbala97.github.io/CyberTechHea...
You will find that it is surprisingly easy just watch this video by Grant Ongers.
m.youtube.com/watch?v=XXTP...
#cybersec #appsec #owasp #infosec #threatmodeling #cornucopia #gameification