
The first of a four-part Inside Microsoft Threat Intelligence miniseries gives behind-the-scenes look at how Microsoft's Digital Crimes Unit disrupted Storm-1152: msft.it/63327sWnGF
The first of a four-part Inside Microsoft Threat Intelligence miniseries gives behind-the-scenes look at how Microsoft's Digital Crimes Unit disrupted Storm-1152: msft.it/63327sWnGF

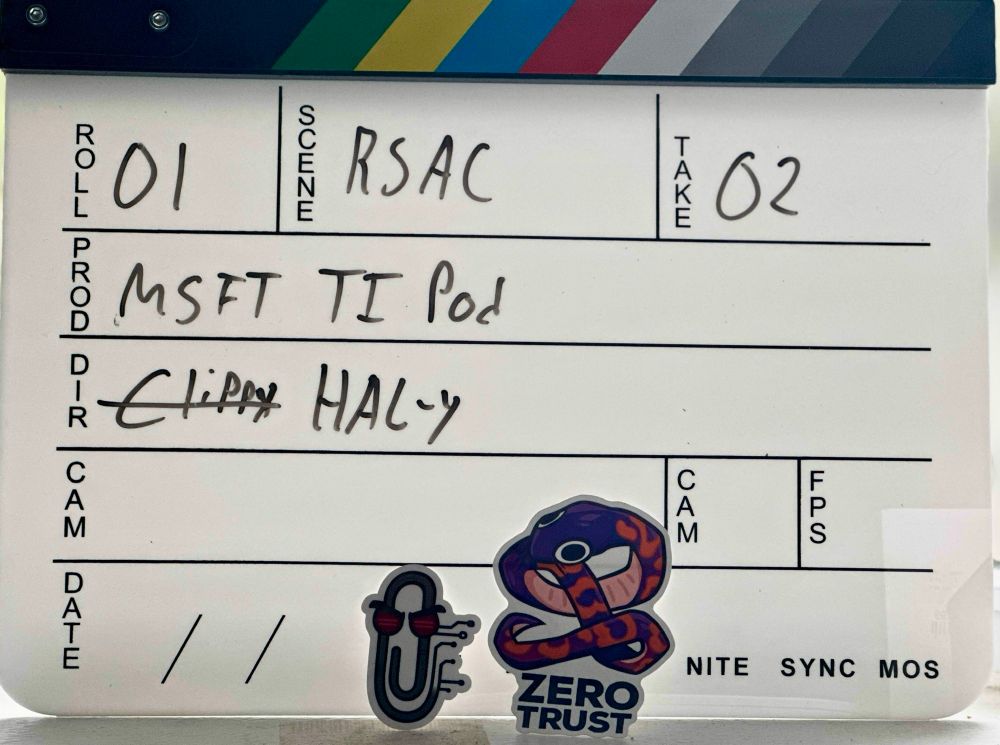
Going for round two, and having MSRC’s podcast takeover, Blain Hailemariam running KC7, and I’ll be moderating a few chats in between.
Going for round two, and having MSRC’s podcast takeover, Blain Hailemariam running KC7, and I’ll be moderating a few chats in between.



From a reliable source. MITRE support for the CVE program is due to expire tomorrow. The attached letter was sent out to CVE Board Members.
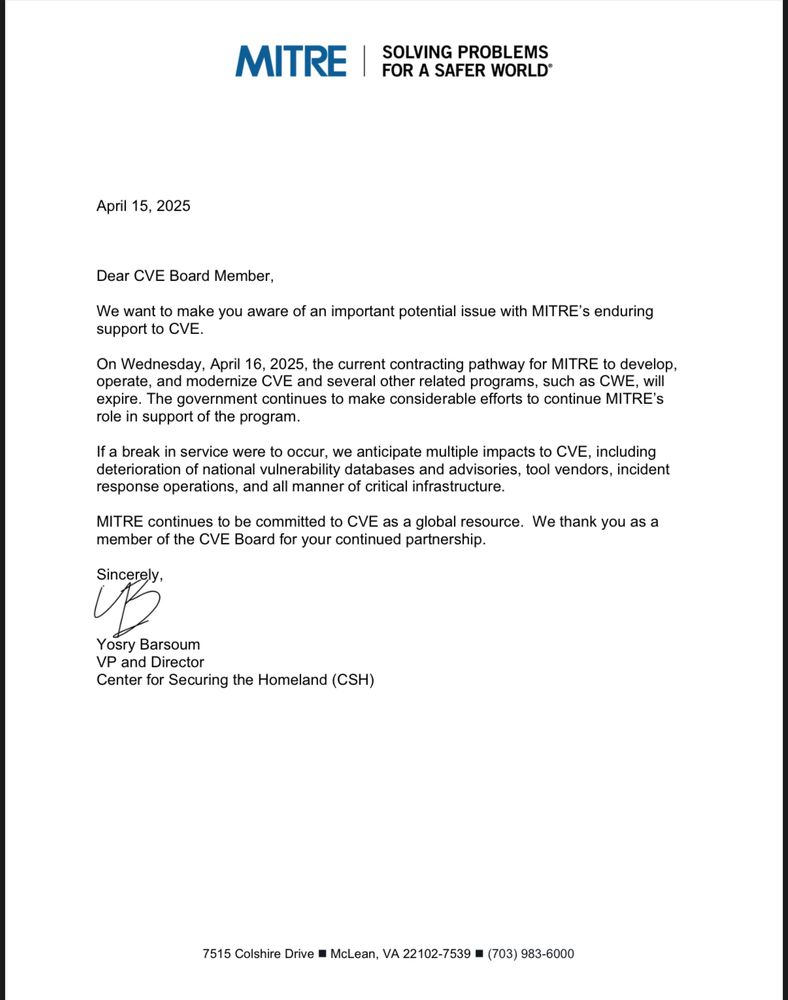
From a reliable source. MITRE support for the CVE program is due to expire tomorrow. The attached letter was sent out to CVE Board Members.







